Preventing DNS Attacks: How to Safeguard Your Brand's Website
The Domain Name System (DNS) plays a pivotal role in a website's functionality and deployment. The DNS provides the critical translation of human-readable domain names like example.com to the underlying IP addresses that computers need to route traffic.
Without a correctly functioning DNS infrastructure mapping domains to the correct web server address, websites will fail to load correctly. Given that the DNS is primarily responsible for ensuring sites can load properly and are available, it has become a prime target for disruptive and damaging cyber attacks. According to IDC's 2022 Global DNS Threat Report, 88% of businesses experienced at least one DNS attack, costing an average of about $942,000.
Cybercriminals can redirect website traffic to malicious servers to steal data or install malware by infiltrating DNS records and infrastructure through sophisticated techniques like domain hijacking and cache poisoning.
This is why businesses must take proactive measures to protect their website and brand and understand the severity of these types of threats. There are several best practices to implement to safeguard your domain, from deploying 24/7 cyber incident response and monitoring to isolating your infrastructure. This short guide outlines ways for preventing DNS attacks and how to detect and protect your estate.
Table of Contents
What is a DNS Attack?
The DNS acts like a phone book for the internet, translating readable domain names into IP addresses that computers can understand. It's like matching phone numbers and country codes with the relevant addresses and names of the holders. DNS servers maintain swathes of records that match domains to their correct IPs.
DNS cache poisoning or DNS spoofing attacks work by infiltrating these records to redirect traffic away from legitimate servers.
For example, a hacker may change the IP address tied to your company's domain name to point to their malicious server instead of your website. Anyone visiting your domain would unknowingly be sent to the hacker's version, meaning login credentials could be stolen or malware could be installed onto the visiting device.
It's not uncommon to see spoofed websites that mirror the ‘real' version closely, fooling users into thinking they are accessing a trusted resource.
Common DNS Attack Techniques

Hackers use various methods to infiltrate DNS records and caches:
DNS Cache Poisoning
In DNS cache poisoning, the attacker tricks the DNS resolver into caching false or malicious information, resulting in the resolver sending the wrong IP address to clients and redirecting users to the wrong place, often to malicious or dangerous sites.
DNS Hijacking
With DNS hijacking, hackers intentionally manipulate how DNS queries are resolved. This can be done by installing malware on user PCs or seizing control of DNS connections or routers, redirecting users to malicious sites.
DNS Tunneling
In DNS tunnelling, attackers use the DNS protocol to create a covert channel for data exfiltration. Rather than using DNS requests and replies for legitimate IP address lookups, the malware uses them to implement commands.
Domain Shadowing
Hackers use compromised domain registrar accounts to create fake subdomains that impersonate or ‘shadow' legitimate domains. Traffic gets redirected through these fake shadow domains to malicious sites.
Dangers of DNS Attacks
DNS attacks are often motivated by financial gain or political leverage, with cybercriminals intent on distributing malware, stealing data, or causing service disruption.
If successful, they pose serious risks to users and organisations, including:
- Loss of service: If your website is inaccessible due to DNS spoofing, you could experience costly downtime and lost income. Many customers would be unable to access your site or buy any products, and if they do, there is a risk that their funds are being distributed to false recipients.
- Phishing or malware: If hackers gain access to your domain, they can convincingly phish for sensitive data across your infrastructure by emailing suppliers, stakeholders, or customers, disguising themselves as your brand. Alternatively, they could result in malware installations on all connected user devices for spying or crypto-mining.
- Reputational damage: DNS attacks are pretty severe, and if businesses are known to have suffered one, where customer data, financial information, credentials and personal details have been leaked or ended up on a spoofed site, it can reflect poorly on the business that's been affected. Such damage to a brand's reputation can profoundly affect customers, investors, and turnover.
- Regulatory or compliance fines: Businesses in heavily regulated industries like finance or healthcare may be fined if sensitive data is compromised. Companies can face penalties for failing to exercise due diligence, care and skill in safeguarding account holders' personal information under frameworks issued by GDPR, the FCA, HIPAA, and others.
How to Detect DNS Attacks
Defending against DNS threats requires regular monitoring of your DNS infrastructure for signs of anomalous or unlawful activity.
Here are critical signals to watch for:
- Unexpected changes in DNS records: Closely track changes made to your domain's DNS records for anything suspicious. Consider enabling notifications for any changes to verify their legitimacy.
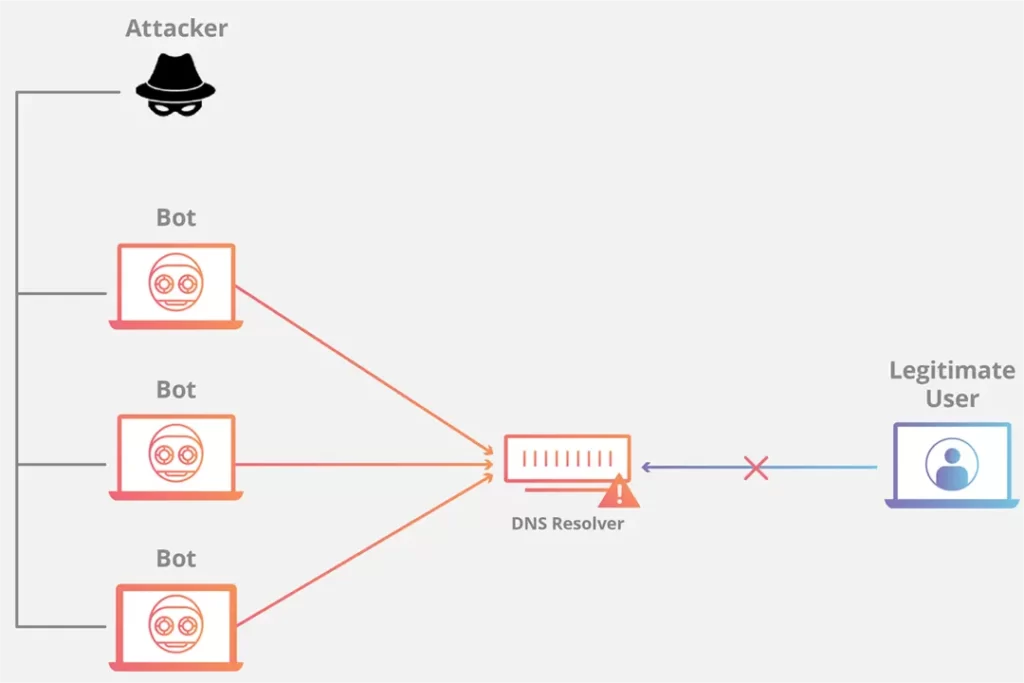
- Traffic spikes: If traffic to your domain suddenly spikes without explanation, it could indicate a DDoS (distributed denial-of-service) attack is in progress to overwhelm servers.
- Slow performance: If servers are overwhelmed, it can sometimes slow down DNS request responses for clients, which could indicate an attack.
- Requests from unfamiliar ranges: Watch for DNS queries from unusual IP addresses. Most requests should originate from your known user base, whereas those requests from further afield could indicate suspicious activity.
- DNS errors: Monitor for mistakes like missing records or unexpected timeouts, as consistent patterns of this activity could tell that poisoning is happening.
Preventing DNS Attacks: Infrastructure

There are several best practices you can implement to safeguard your DNS infrastructure against exploits:
Deploy Cyber Response and Monitoring Solutions
Ensure that your organisation has a stable and reliable emergency cyber incident response plan ready to contain and mitigate attacks if one occurs. If malicious actors remain in a system or network for long periods, it can worsen damage, so swift and proactive action is critical. You can even look to third-party penetrating testing specialists that can simulate a DNS attack and test its robustness.
Use DNSSEC
The Domain Name System Security Extensions feature authenticates responses to domain name lookups. It's a form of two-factor authentication, ensuring any requests come from authorised, verified sources. This prevents any hackers from forging DNS records.
Restrict User Permissions
Limit who can edit your DNS zone records to prevent unlawful or unverified tampering. Ensure that each user is verified before access is granted.
Isolate Infrastructure
Ensure your DNS servers are segmented away from your other infrastructure and backed up with firewalls and stringent security software. This will make them more difficult for attackers to reach and compromise.
Actively Monitor Traffic
To detect anomalous activity, enable real-time monitoring solutions on DNS query patterns, volumes, sources, and other telemetry. Enable notifications for any suspicious or unusual activity, and report any odd patterns.
DNS attacks threaten your website and brand's availability, security, and integrity. However, taking proactive steps to strengthen your DNS environment is crucial for protecting your assets, devices and customer data from these evolving and insidious threats. By being prepared to respond quickly and diligently, you'll be making a valiant effort in combating cybercrime.
Wrapping Up
In summary, DNS attacks seriously threaten any organisation's online presence and brand reputation. By implementing DNSSEC, regular monitoring, and proper DNS hygiene practices, companies can help prevent successful spoofing, cache poisoning, and other malicious actions. IT and security leaders must understand the most common DNS attack vectors, regularly patch and update their DNS infrastructure, use registrars that support DNSSEC, and work with a reliable DNS hosting provider.
With cyberattacks on the rise, every brand must pay attention to the importance of DNS security. By proactively safeguarding their DNS infrastructure and servers, organisations can protect their domain names, websites, email, and other services from being compromised. Protecting your DNS should be considered a fundamental component of an overall cybersecurity strategy. The risks associated with weak or vulnerable DNS servers are too significant. By following the best practices outlined here, companies can help minimise their attack surface, maintain customer reliability, and preserve trust in their brand.