10 Cybersecurity Best Practices for Protecting Your Business
The question isn’t if you’ll be targeted; it’s when.
A single breach can destroy a business overnight, and hoping it won’t happen to you is a strategy for failure.
The cybersecurity best practices in this guide aren’t just “tips”; they are a layered defence system.
This isn’t a boring legal manual.
It’s a strategic breakdown of the 10 actions required to build an ironclad operation, from employee training to data encryption, that will protect your business and your bank account.
- Cybersecurity is essential: Protects customer trust, prevents financial loss, and ensures smooth business operations.
- Training and awareness: Regular training sessions empower employees to recognise threats and prevent breaches.
- Proactive measures: Implement tools like multi-factor authentication, firewalls, and regular data backups to enhance security.
- Leadership involvement: Committed leadership fosters a strong cybersecurity culture and encourages all employees to prioritise safety.
- Collaborate with experts: Engaging cybersecurity specialists can provide insights and reinforce measures against evolving threats.
The Importance of Cybersecurity for Your Business

Cybersecurity isn’t just about firewalls and antivirus software. It’s a comprehensive strategy for protecting your data, finances, and reputation. Here’s why it’s critical for your business:
- Protecting Customer Trust: Your customers expect you will handle their data responsibly. A breach can erode that trust and directly impact your bottom line.
- Preventing Financial Loss: A small business’s average cost of a cyberattack can be substantial, often exceeding £100,000. This could mean the difference between profits and losses.
- Ensuring Business Continuity: Cyberattacks can shut down your operations. Investing in cybersecurity helps you operate smoothly and consistently.
- Regulatory Compliance: With the rise of data protection laws such as GDPR, ensuring secure operations isn’t just good practice; it’s a legal obligation.
Understanding the cybersecurity landscape is vital. Look around you; every click you make, every email you send, holds potential risks. But here’s the good news: you can significantly reduce those risks with the right strategies.
The UK Gold Standard: Cyber Essentials and Beyond
For any UK business, the journey toward security is defined by two primary frameworks: Cyber Essentials and ISO/IEC 27001. These are not just badges for your website; they are structured methodologies to ensure your “digital front door” is locked.
Cyber Essentials is a government-backed scheme that focuses on five technical controls: firewalls, secure configuration, user access control, malware protection, and patch management. If you are bidding for government contracts, this certification is often mandatory.
Cyber Essentials Plus takes this a step further by requiring a hands-on technical verification.
In contrast, ISO 27001 is an international standard for an Information Security Management System (ISMS). It is more rigorous, covering people, processes, and technology.
| Feature | Cyber Essentials | ISO 27001 |
| Primary Focus | Technical baseline security | Holistic risk management |
| Best For | SMEs & Government contractors | Mid-market & Global Enterprises |
| Certification | Self-assessment + external scan | Comprehensive 3rd party audit |
| Renewal | Annual | 3-year cycle with annual checks |
Pro Tip: If you are an SME, start with Cyber Essentials. It provides the most immediate “bang for your buck” and meets the majority of requirements for small-business insurance providers.
Your First Steps Towards Cybersecurity
You might feel overwhelmed by the thought of diving into cybersecurity. After all, it sounds complicated and technical. But let’s break it down into manageable steps.
Think of it as building muscle; you don’t run a marathon without training. Start by adopting a few foundational practices:
- Educate Yourself and Your Team: Knowledge is your first line of defence. Make cybersecurity awareness training an ongoing initiative. Regular quick refresher sessions every quarter can help keep the topic fresh in everyone’s mind.
- Develop a Cybersecurity Plan: Outline your approach, including detection, protection, and response strategies, and leverage tools such as fraud detection software to enhance security. A written plan helps you organise thoughts and prepare for potential breaches.
- Make it a Team Effort: Cybersecurity doesn’t just sit with the IT department. It’s the responsibility of every employee. Encourage everyone to take ownership and make security a part of their daily routine.
Consider this: an employee who falls for a phishing email can open the gates to your system. You want each person in your organisation to think like a gatekeeper. They must be aware of the threats and know how to respond.
The Tools You Need
Let’s talk tools for a moment. Security software is essential, but don’t get bogged down with flashy products. Here are some tools that will make a real difference:
- Antivirus Software: This should be your first line of defence; always keep it up to date.
- Firewall: A firewall decides what traffic can enter and exit your network. Make sure it is active and properly configured.
- VPNs (Virtual Private Networks): VPNs enhance the security of your internet connection, especially when working remotely.
- Backup Solutions: Regular data backups can help protect your business from ransomware attacks. Select solutions that automate your backups and simplify restoration.
- Password Managers: Utilise these tools to create and securely store strong, unique passwords for all your online accounts.
Now, bear in mind that tools are just part of the equation.
| Security Layer | Traditional Tool (Legacy) | Utilises machine learning to detect and block unknown “Zero-Day” threats. | Why Upgrade? |
| Endpoints | Standard Antivirus | EDR/XDR (e.g., SentinelOne) | Uses Machine Learning to stop unknown “Zero-Day” threats. |
| Access | Passwords | Passkeys & Biometrics | Eliminates Phishing by removing the “knowledge” factor. |
| Network | Basic VPN | SASE (Secure Access Service Edge) | Provides faster, encrypted access with Identity-Aware routing. |
| Training | Annual Video Course | Continuous Simulation | Tests employees with Deepfake Voice and AI Phishing in real-time. |
The 10 Essential Cybersecurity Best Practices
You’ve grasped the gravity of the cybersecurity landscape, and it’s clear: the time for action is now.
Protecting your business from threats isn’t optional; it’s essential. So, let’s zoom in on the ten best practices you can implement today. These steps will fortify your digital environment and help you fend off would-be intruders.
1. Advanced Awareness: Beyond “Spotting the Typos”

In 2026, the era of “broken English” phishing emails is over. Cybercriminals now use Generative AI to craft perfect lures and, more dangerously, Deepfake audio and video. An employee may receive a WhatsApp voice note that sounds exactly like the CEO requesting an urgent “off-ledger” payment to a new vendor.
Establishing “Proof of Life” Protocols
To counter these high-tech scams, your team needs more than a video course. Implement a Proof of Life protocol for all sensitive financial transactions:
- Shared Secrets: Establish non-digital code words for high-risk actions.
- Multi-Channel Verification: If an “urgent” request comes via Slack, verify it by phone with a known number.
- Linguistic Anomalies: Train staff to look for slight changes in tone. Even the best Large Language Models (LLMs) can struggle with hyper-local company culture or internal shorthand.
Example Scenario: A finance manager at a London-based creative agency received a video call from the “Managing Director” requesting a £50,000 transfer for a “secret acquisition”. The manager, trained in Social Engineering red flags, asked a specific question about the office dog. The AI failed to answer, exposing the deepfake before any funds were lost.
2. Beyond Antivirus: EDR, XDR, and MDR Explained
The “antivirus” of ten years ago looked for known “signatures” of viruses. Today’s threats are “fileless”, meaning they live in your computer’s memory and leave no trace on the hard drive. To stop them, you need behaviour-based detection.
- Endpoint Detection and Response (EDR): Tools like SentinelOne or CrowdStrike Falcon monitor your laptops and servers for suspicious behaviour (e.g., a spreadsheet suddenly trying to encrypt your files).
- Extended Detection and Response (XDR): This connects your email security, network firewalls, and endpoints into one single view. It shows that a suspicious email led to a suspicious login, which then led to a file being downloaded.
- Managed Detection and Response (MDR): This is the “human” version. You outsource the monitoring to a Security Operations Centre (SOC) that watches your systems 24/7.
Which is right for you? If you have a dedicated IT person, EDR is sufficient. If you are a high-growth firm with no dedicated security staff, MDR is the gold standard for 2026, providing enterprise-grade protection at a fraction of the cost of a full-time hire.
3. Implement Multi-Factor Authentication (MFA)
Here’s where things get a bit techy, but stay with me! Multi-factor authentication (MFA) adds an extra layer of security to your setup. Users must verify their identity through multiple methods before accessing systems or data.
- What It Looks Like: After entering a password, users might receive a text message with a code they need to join to gain access. This makes it incredibly challenging for hackers, even if they steal passwords.
- Benefits of MFA: Statistics show that MFA can block 99.9% of automated cyberattacks. It’s like having a bouncer at your digital nightclub—not just anyone can get in!
Make MFA a mandatory step for accessing sensitive accounts. This simple practice can drastically fortify your security posture.
The Architecture of Distrust: Implementing Zero Trust
The concept of a “trusted internal network” is a relic. Modern businesses must adopt Zero Trust Architecture (ZTA). Under this model, every access request—whether from the office in Manchester or a remote worker in Spain—is treated as a potential breach.
The Three Pillars of Modern Identity
To build a Zero Trust environment, you must move beyond the password.
- Identity Providers (IdP): Use tools like Okta or Microsoft Entra ID (formerly Azure AD) to centralise user logins.
- Passkeys and FIDO2: In 2026, SMS-based codes are vulnerable to SIM Swapping. Transition your team to Passkeys or physical Hardware Security Keys like the YubiKey. These are phishing-resistant because they require physical possession.
- Context-Aware Access: Your system should automatically block a login attempt at 3:00 AM from an IP address in a country where you have no employees.
Implementation Step: Start by mapping your “Protect Surface”—the specific data (customer lists, financial records) that is most valuable. Apply Zero Trust to these assets first before rolling it out to the entire network.
4. Use Firewalls to Protect Your Network
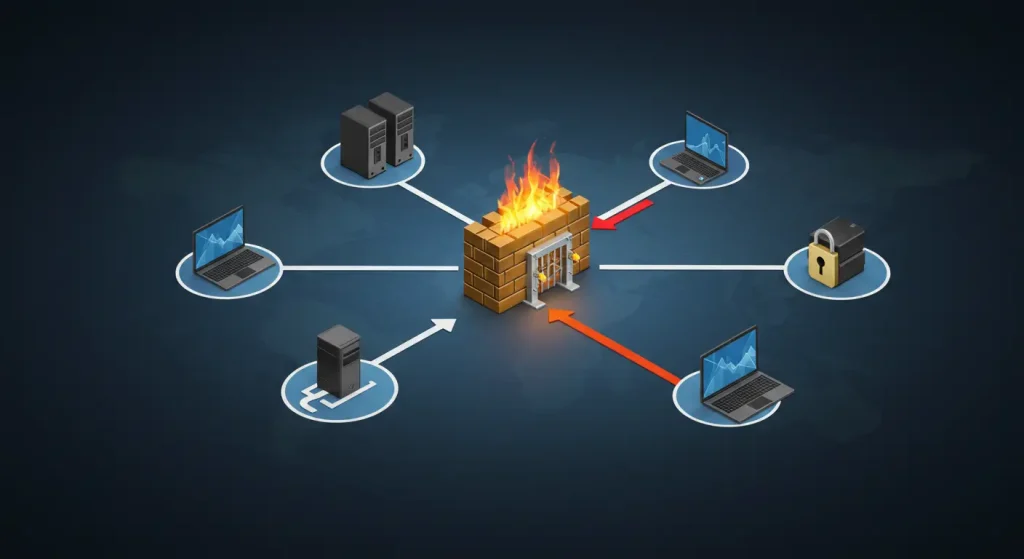
Firewalls are your digital barriers. Think of them as gates that regulate incoming and outgoing traffic. They don’t allow all traffic to pass through blindly; they inspect it first.
- Types of Firewalls: You can choose software firewalls for individual machines or hardware firewalls for the entire network. The latter is often more effective for protecting against external threats.
- Configuration Counts: Ensure your firewall is configured correctly. Take the time to adjust settings according to your specific needs. Don’t worry—you don’t have to be a network engineer; many guides are available online to walk you through the process.
Imagine your firewall as a trusty guard dog. With a well-trained dog, intruders may think twice before trespassing. The same goes for your firewall!
5. Secure Wi-Fi Networks
Let’s talk about your wireless network. If it’s insecure, you might leave the door wide open. Here’s how to lock it down:
- Change Default Passwords: Many routers come with default usernames and passwords. One of the first things you should do is replace these with stronger, more unique ones.
- Use WPA3 Encryption: If your router supports it, enable WPA3. This is the most secure Wi-Fi encryption, offering protection against unauthorised access.
- Hide Your Network: Consider hiding the SSID (network name) to make it less visible to outsiders. While not foolproof, it can deter casual hackers.
A securely set up Wi-Fi network reduces the risk of others using your internet for malicious purposes and helps keep your data safe.
6. Regularly Back Up Critical Data
Data loss can happen due to accidents, ransomware, or hardware failure. Regular backups are crucial.
- Backup Solutions: Utilise cloud services to automatically back up vital data. Platforms like Google Drive and Dropbox can provide excellent solutions for seamless backups.
- Local Backups: In addition to cloud backups, keep physical copies on external hard drives or USB drives, which you can disconnect and store away when not in use.
Consider this metaphor: if a fire broke out in your office, would you have a plan to save your critical documents? Regular backups serve as your safety net in the event of a potential calamity.
7. Create a Mobile Device Security Plan

In today’s world, mobile devices are ubiquitous. Work doesn’t just happen in the office anymore—employees are often on the go, accessing sensitive information from their phones.
- Set Policies: Establish guidelines for accessing company data from personal devices. Consider requiring encryption and remote-wipe capabilities for added security.
- App Management: Encourage employees to download only credible apps. Scammers often use malicious apps to steal data.
- Regular Updates: Just as antivirus software needs to be updated, so do mobile operating systems. Prompt employees to regularly update their devices.
Developing a mobile security plan helps reduce the risk of data breaches resulting from lost or stolen devices.
8. Conduct Regular Risk Assessments
Risk assessments are essential for identifying potential vulnerabilities in your cybersecurity plan.
- What to Include: Review your security measures and employee practices, and regularly evaluate your software and hardware. Include software asset management to keep track of all software in use and detect outdated or unauthorised applications.
- Engage Experts: Bring in cybersecurity consultants who can provide objective insights and recommendations for improvement.
- Action Plan: Once you have gathered data, create an actionable plan to address the identified weaknesses. Think of it as an annual health check-up for your business’s cyber health.
Regular assessments keep your business resilient against threats. After all, you wouldn’t skip your health check-up, would you?
9. Securing the Chain: NIS2 and Third-Party Risk
Your business is only as secure as the weakest software vendor you use. The NIS2 Directive (and its UK equivalents) has expanded the scope of infrastructure considered “essential” or “important”. If you provide services to larger firms, they will now audit your security as part of their own compliance.
The Software Bill of Materials (SBOM)
When purchasing new software, ask for an SBOM. This is essentially an ingredient list for software. It tells you exactly which open-source libraries are used in the product, so you can react instantly if a new vulnerability (like the 2021 Log4j crisis) is discovered.
Vendor Vetting Checklist
Before signing a contract with a SaaS provider, verify the following:
Incident Notification: Will they notify you within 24 hours of a breach?
SOC 2 Type II Report: Evidence that they manage your data securely.
Data Residency: Does the data remain in the UK/EU to comply with GDPR?
10. Invest in AI-Powered Cybersecurity Tools
Finally, let’s talk tech. Artificial Intelligence (AI) is revolutionising the cybersecurity landscape. Consider investing in AI-powered tools that can help:
- Threat Detection: AI can analyse vast amounts of data, spotting anomalies faster than a human could.
- Automated Responses: Certain AI tools can provide prompt responses to threats, thereby reducing the need for human intervention.
- Improvements Over Time: The beauty of AI is that it learns. As it gathers data, it gets better and more efficient at spotting threats.
Imagine having a security guard who never sleeps. AI tools can act as that vigilant sentinel for your business, tirelessly monitoring and adapting.
Implementing these ten essential cybersecurity best practices lays a strong foundation for protecting your organisation. The cyber realm is fraught with risks, but being proactive puts you in a position of control.
These practices are not just a checklist; they are critical steps toward creating a secure environment for you, your employees, and your customers. Don’t wait until it’s too late—take action today!
When the Worst Happens: The Incident Response Playbook
Success in cybersecurity is not just about prevention; it’s about Resilience. When a breach is detected, the first 60 minutes are critical. You must have a pre-written Incident Response Plan (IRP).
Immediate Action Steps
- Isolate: If a laptop is acting strangely, disconnect it from the Wi-Fi immediately. Do not shut it down—forensic experts may need the data in the RAM.
- Verify: Determine if it’s a false alarm or a genuine Data Breach.
- Notify: Under UK GDPR, if personal data is compromised and likely to result in a risk to individuals, you must notify the Information Commissioner’s Office (ICO) within 72 hours.
- Communicate: Have a draft email ready for your customers. Transparency builds trust; silence destroys it.
The “1-10-60” Rule: Aim to detect an intruder within 1 minute, investigate within 10 minutes, and isolate them within 60 minutes.
Building a Cybersecurity Culture

As we transition from essential best practices to a pivotal area of focus, let’s discuss building a cybersecurity culture within your organisation. This isn’t just about implementing measures; it’s about ingraining security into the very fabric of your business.
Think of it as adopting a healthy lifestyle; it’s not just about the occasional workout but embracing a holistic approach. Let’s explore how you can foster a culture that prioritises cybersecurity every single day.
Employee Engagement
First up is employee engagement. Every team member plays a crucial role in defending your business against cyber threats. But how do you get everyone on board?
- Gamify Training: Regular training is essential, but make it fun. Engage employees through gamified modules that reward learning and motivate continued learning. Incorporate quizzes, leaderboards, and challenges. One company I worked with introduced a monthly cybersecurity quiz, and they saw a noticeable increase in engagement. Employees loved the competitive edge!
- Create Cyber Champions: Identify individuals in your organisation who are passionate about cybersecurity. Empower them as “cyber champions” or “security advocates.” They can lead initiatives, remind teammates of best practices, and serve as a point of contact for questions.
- Open Discussions: Make cybersecurity a topic of regular conversation. Schedule roundtable discussions or lunch-and-learn sessions where employees can share their ideas, concerns, or experiences related to cybersecurity. This approach will help demystify complex issues and foster a supportive environment.
When employees feel involved and valued, they become more vigilant and proactive. It’s all about making them part of the security narrative.
Leadership Commitment
Next is the crucial aspect of leadership commitment. Without leadership support, your cybersecurity initiatives may fall short of expectations. Strong commitment from the top can set the tone for your entire organisation.
- Lead by Example: Make sure leadership practices good cybersecurity habits. Simple actions, such as using strong passwords or enabling multi-factor authentication, demonstrate to employees that security is a priority across the board.
- Allocate Resources: Leaders need to prioritise cybersecurity by dedicating sufficient resources, including budget and personnel. Investing in tools or training isn’t just a line item; it’s an investment in the business’s future.
- Set Expectations: Establish clear cybersecurity policies and communicate them effectively to ensure a consistent approach across the organisation. Don’t just throw them in an employee handbook; discuss them in meetings and gather input from your team. Setting expectations fosters accountability.
Remember, when leaders prioritise cybersecurity, it sends a message that protects every aspect of the business’s reputation and integrity. Employees will take cues from leadership, so make your commitment transparent and steadfast.
Collaborating with Experts
Let’s face it: cybersecurity isn’t easy. The threat landscape evolves rapidly, and it often feels like the bad actors are one step ahead. This is where collaborating with experts comes into play.
- Consultants and Specialists: Engage external cybersecurity consultants to evaluate your business. They can offer an objective perspective and identify vulnerabilities you may not have considered. Their expertise can help you refine and improve your security policies.
- Require External Audits: Engage third-party auditors to periodically review your systems, as this can provide invaluable insights. An external set of eyes can highlight blind spots and offer recommendations for improvement.
- Stay Informed: Attend webinars, conferences, and industry events where cyber experts gather. Networking with professionals not only helps you stay updated on trends and threats but may also provide you with potential partners for collaboration.
By leveraging external expertise, you can introduce fresh ideas and strategies into your organisation, enhancing your overall cybersecurity approach.
Outsourcing IT Security
Now, let’s consider outsourcing IT security. It’s no longer just a trend but a common practice for many companies.
- Managed Security Service Providers (MSSPs): These organisations provide employees with 24/7 monitoring, detection, and response services. They’re effective because they stay up to date on global threats and can react more swiftly than an in-house team.
- Cost-Effective Solutions: For SMBs, outsourcing can be a more cost-effective solution than hiring full-time IT security staff. Adding talent can quickly drain resources, so why not utilise outside expertise?
- Focus on Core Business: By outsourcing, your team can concentrate on core business functions while entrusting cybersecurity to trained professionals. This boosts productivity and makes your employees more effective in their primary roles.
When enhancing your company’s cybersecurity framework, consider the strength that an effective partnership built through a Request for Proposal process can bring.
Organisations often overlook the need to establish clear expectations with their service providers.
For businesses seeking to partner with Managed Security Service Providers (MSSPs), preparing and following a detailed cybersecurity RFP template can help identify the best fit.
This enables businesses to advocate effectively while ensuring that comprehensive security measures are in place. The meticulous documentation not only clarifies needs but also significantly improves decision-making.
Outsourcing doesn’t mean relinquishing control; it’s about gaining a partnership that enhances your security landscape.
Continuous Improvement
Finally, let’s discuss the concept of continuous improvement. Cybersecurity isn’t a set-it-and-forget-it realm. It’s a journey. As the saying goes, “If you’re not moving forward, you’re falling behind.”
- Regular Training Updates: Cybersecurity threats are consistently evolving. Regularly update training materials to reflect the latest threats and best practices. Short refresher courses can help keep your team’s knowledge fresh.
- Incident Response Drills: Conduct regular drills to ensure your team knows how to respond to cyber incidents. This will create confidence and preparedness.
- Feedback Loop: Encourage employees to share their thoughts on current practices and procedures. Creating opportunities for feedback fosters a culture of continuous improvement. Employees often have insights that leadership might overlook.
- Monitor Industry Trends: Stay current on cybersecurity news and advancements in security tools and technologies. Implementing new technologies and practices can give you an edge over potential threats.
By embedding a continuous improvement mindset, you make security an evolving part of your business strategy. This readiness will help you avoid cyber threats and protect what matters most.
Building a culture of cybersecurity isn’t just about policies or tools—it’s about fostering an empowered, engaged team that prioritises safety at every level. Each element contributes to a robust defence against cyber threats, from employee engagement to leadership commitment.
Remember, a secure organisation starts with a shared commitment to maintaining and improving cybersecurity.
Make it a journey for everyone in your company because together, you can cultivate a safe and resilient business for the future.
Conclusion

Having journeyed through the critical aspects of building a solid cybersecurity foundation, we arrive at an essential consideration: the cost of inaction.
The cybersecurity landscape is fraught with risks that can lead to catastrophic consequences for your organisation. As you contemplate your next steps, let’s discuss why taking action is crucial and the potential consequences of doing nothing.
The Reality of Cyber Threats
At this point, it’s worth reiterating just how real and pressing the threat of cybercrime is. Reports indicate that cyberattacks are increasing in frequency, sophistication, and financial impact.
Hold onto your seats: In 2023 alone, global cybersecurity breaches covered by the media cost businesses nearly $3 trillion!
Here’s what you risk if you fail to prioritise cybersecurity:
- Financial Loss: The immediate financial repercussions of a cyber breach can lead to escalating recovery costs. The numbers can add up quickly, whether it’s paying ransoms, legal expenses, or fines due to non-compliance with data protection laws. Some businesses even face bankruptcy.
- Reputation Damage: Customers expect you to protect their data. A breach can shatter trust and lead to customer attrition. When trust is lost, it can take years to rebuild, even if the damage can be recovered from. Think about it: would you continue to patronise a business that compromised your data?
- Operational Downtime: A cyber incident could halt your operations as you scramble to address the breach, potentially causing significant disruptions. Downtime during an attack or recovery can significantly reduce productivity and revenue.
- Legal and Regulatory Consequences: With the emergence of stringent data privacy laws worldwide, failing to protect customer data can result in fines and penalties. For instance, GDPR violations can result in significant financial penalties of millions. Would you risk putting your company in such a vulnerable position?
Given these facts, the question becomes: Can you afford the cost of inaction?
The Real Cost of Ignoring Cybersecurity
Ignoring cybersecurity isn’t just harmful; it’s a high-stakes gamble. Picture this: a small business that underestimated the significance of cybersecurity suddenly falls victim to a ransomware attack. They discover that their entire system is locked and face a substantial ransom demand.
Here’s a breakdown of the potential fallout from ignoring cybersecurity measures:
- Financial Costs
- Direct Costs: Legal fees, ransom payments, and system recovery costs.
- Indirect Costs: Loss of business, reduced productivity, and reputational damage.
- Loss of Trust
- Customer Loyalty: Customers are likely to take their business elsewhere, which can negatively impact sales.
- Employee Morale: A breach can create anxiety and distrust among employees.
- Regulatory Ramifications
- Fines: Failure to comply with regulations can result in severe penalties.
- Litigation: Customers may sue for the mishandling of their data.
With stakes this high, it becomes clear that assuming “it won’t happen to me” is not only naive but also shortsighted.
Benefits of Taking Action
On the flip side, there’s incredible value in taking proactive steps to enhance your cybersecurity posture. Acting now provides not only protection but also peace of mind. Here’s what you stand to gain by making investments in cybersecurity:
- Increased Confidence: Knowing you have measures to protect your assets can boost confidence among employees, clients, and stakeholders.
- Enhanced Reputation: Demonstrating a commitment to cybersecurity can differentiate you from competitors and offer a strong value proposition to customers concerned about data protection.
- Long-term Cost Savings: Investing in cybersecurity upfront may save you substantial amounts in the long run. Prevention is always more cost-effective than recovery.
- Adaptability and Resilience: A strong cybersecurity framework allows you to respond more effectively to incidents when they occur, reducing response time and minimising damage.
FAQs
What is the average cost of a data breach for a UK SME in 2026?
The average cost has climbed to approximately £145,000. This figure includes not just the technical recovery but also legal fees, loss of business during downtime, and the inevitable spike in Cyber Insurance premiums.
Can hackers bypass Multi-Factor Authentication (MFA)?
Yes. Techniques like MFA Fatigue (bombarding a user with login requests until they click ‘Approve’ out of annoyance) or Session Hijacking are common. This is why moving to “Number Matching” or physical Hardware Keys is the recommended standard for 2026.
Should my small business pay a ransomware demand?
The NCSC and police strongly advise against it. Paying does not guarantee you will get your data back, and it marks your business as a “soft target” for future attacks. Focus instead on robust, offline Backups that allow you to restore without the hackers’ help.
Is a VPN enough to protect my remote workers?
In 2026, a VPN is only one piece of the puzzle. While it encrypts the “tunnel,” it doesn’t verify the device’s health or the user’s identity. Most firms are moving toward SASE (Secure Access Service Edge), which combines VPN capabilities with Zero Trust security.
How do I report a cybercrime in the UK?
For immediate threats, contact Action Fraud (the UK’s national reporting centre for fraud and cybercrime). If personal data is involved, you must also report the incident to the ICO via their online portal.

