Mobile App Marketing Guide: Strategies and Tools
Building an app is the easy part. Getting people to download it, keep it, and eventually pay for it? That is a war of attrition.
There are over 5 million apps available across the Apple App Store and Google Play Store. The “build it, and they will come” philosophy is not just optimistic; it is negligent.
I have sat across the table from founders who spent their entire budget on development, leaving £500 for marketing, expecting to be the next Uber. It does not happen.
Effective app marketing is not about hoping for a viral hit. It is a forensic combination of data science, psychological triggers, and relentless optimisation.
It requires understanding that your competition isn’t just other apps in your category; it’s the finite attention span of a human being who checks their phone 144 times a day.
This guide ignores the “make a Facebook page” junk. We are examining the technical, creative, and financial infrastructure necessary to scale a mobile application in a highly competitive market.
- Optimise your App Store page first; ASO drives free visibility and improves Page View to Download conversion.
- Integrate a Mobile Measurement Partner; accurate attribution is essential for scaling and calculating LTV versus CAC.
- Prioritise retention through excellent FTUE, permission priming, and personalised push messaging to reduce churn.
- Run paid UA with diverse channels and a creative factory; refresh creatives frequently to avoid rapid fatigue.
- Design for privacy forward measurement; adapt to SKAdNetwork and Google Privacy Sandbox to remain effective.
What is App Marketing?
App marketing is the continuous process of attracting users to your mobile application (Acquisition), ensuring they find value immediately (Activation), and keeping them engaged long enough to generate revenue (Retention).
It operates on a specific mathematical equation:
LTV > CAC
If your Lifetime Value (LTV) per user does not exceed the Customer Acquisition Cost (CAC), you do not have a business; you have a hobby that burns money.
The Three Core Pillars
- Acquisition: Getting a user to the store page and converting them to a download.
- Retention: Preventing the user from deleting the app after one use (Churn).
- Monetisation: Converting usage into revenue (Ads, Subscriptions, or In-App Purchases).
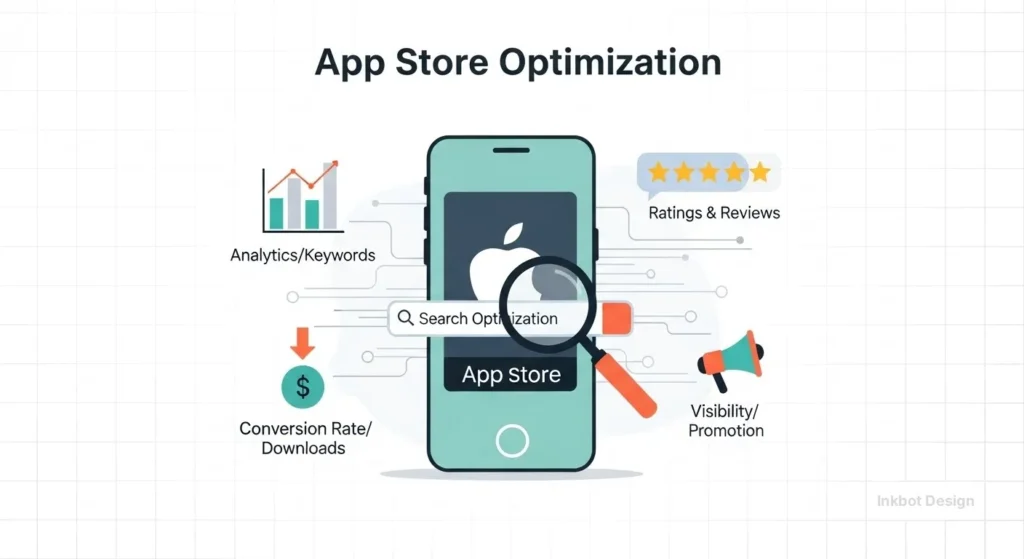
App Store Optimisation (ASO): The Foundation
Before you spend a penny on ads, your “shop window” must be in pristine condition. Sending paid traffic to an unoptimised App Store page is like trying to fill a bucket with a hole in the bottom.
ASO is the SEO of the mobile world. It determines your visibility in organic search and your conversion rate from “Page View” to “Download.”
The Verbal Identity: Keywords and Title
The algorithms used by Apple and Google are semantic, but they behave differently.
- iOS (Apple): Strict. You have a Title (30 characters), Subtitle (30 characters), and a hidden Keyword Field (100 characters). You must be surgical.
- Google Play: Contextual. It scans your Title, Short Description, and Long Description for keyword density, much like web SEO.
The Mistake: Stuffing keywords that you cannot rank for. You will not rank for “Fitness” on day one against MyFitnessPal. You might rank for “Post-natal Yoga Tracker.”
Visual Communication: The Conversion Driver
Your icon and screenshots are not art; they are sales tools.
- The Icon: Must be legible at the size of a fingernail. Avoid text. Use high-contrast colours that stand out against the default white/black backgrounds of system menus.
- Screenshots: Do not just show the UI; also include the content that is displayed. Nobody cares what your settings menu looks like. Use “captioned screenshots” that explain the value proposition.
- Bad: A screenshot of a login page.
- Good: A screenshot of a dashboard with text overlay: “Track your savings in real-time.”
Consultant’s Note: We once audited a fintech client who was using generic “sleek” screenshots. We changed them to feature bold typography, highlighting the specific interest rates and security badges. Their conversion rate increased by 14% overnight. This is the power of communication in marketing.
The Technical Reality: Attribution and MMPs
If you cannot measure it, you cannot scale it. In web marketing, you use Google Analytics. In app marketing, that is not enough. You need a Mobile Measurement Partner (MMP).

Why You Need an MMP
Apple’s App Store and Google Play are “Walled Gardens.” They do not naturally communicate with Facebook, TikTok, or Google Ads to inform them who installed the app. An MMP (like AppsFlyer, Adjust, or Kochava) acts as the neutral referee. They connect the ad click to the app install.
The Post-IDFA World (SKAdNetwork)
Since iOS 14.5, Apple has effectively killed the IDFA (Identifier for Advertisers). This means you can no longer track users individually across apps without their explicit permission.
- The Impact: You cannot see exactly who bought your subscription from a Facebook ad.
- The Solution: You must rely on Apple’s SKAdNetwork. It provides aggregated data with a delay. You get “signals” rather than precise user trails.
If you are launching today, your marketing stack must be built to handle privacy-centric attribution. If you rely on old-school “user-level targeting,” you will fail.
User Acquisition (UA): Paid Strategies
Once your organic presence (ASO) and tracking (MMP) are ready, you turn on the tap. But be warned: Paid UA is expensive.
The Major Channels
| Channel | Best For | Risk Factor | Cost Scale |
| Apple Search Ads | High Intent. Capturing users searching for your competitors. | Low. You pay for relevance. | High CPI |
| Meta (Facebook/Insta) | Scale and Targeting. Visual discovery. | Signal Loss (Post-IDFA). | Medium |
| Google App Campaigns | Automation. Finds users across Search, YouTube, and Play. | “Black Box” (Less control). | Low/Medium |
| TikTok Ads | Virality and Gen Z demographics. | Creative Fatigue (Ads die in 48 hours). | Medium |
The “Creative Fatigue” Death Spiral
On platforms like TikTok and Instagram, an ad creative that works today will stop working in two weeks. Users get bored faster than ever. You must establish a “Creative Factory” that produces new video assets on a weekly basis.
The most successful apps today utilise UGC (User-Generated Content) style ads—videos that resemble native TikToks rather than polished TV commercials. This aligns with modern visual storytelling principles; authenticity converts better than perfection.

Retention: Plugging the Leaky Bucket
Acquiring a user costs between £2.00 and £5.00, depending on the vertical. If they leave after three days, you have lost that money. Retention is the only metric that matters for long-term survival.
The First Time User Experience (FTUE)
The first 60 seconds determine everything.
- Permission Priming: Do not request “Notification Permissions” immediately upon app launch. The user will say no. Explain why they need notifications (e.g., “Get alerted when your order ships”), then trigger the system prompt.
- The “Aha!” Moment: Guide the user to the core value as fast as possible. If it’s a photo editor, get them to edit a photo within three clicks.
Push Notifications: The Double-Edged Sword
Used correctly, Push is a retention weapon. Used poorly, it causes uninstalls.
- Personalisation: “Hey there, come back!” is garbage. “Your file is ready for download” is a useful message.
- Frequency: Data from Airship suggests that retention rates are 3x higher for users who receive push notifications, but there is a tipping point. More than one generic push per week often leads users to disable them entirely.
Brand Narrative and “Virality”
You cannot buy every user. Eventually, you need organic growth, often referred to as the K-factor.
K = i × c
Where i is the number of invites sent by each customer, and c is the conversion rate of those invites. If K > 1, you have exponential viral growth.
However, virality is rarely about buttons. It is about Narrative. Apps like Calm or Headspace didn’t just sell meditation; they sold an antidote to modern anxiety. They developed a strong brand narrative that users wanted to share, signalling their own values.
If your app is purely functional and lacks an emotional branding connection, your users will treat it as a utility—easily replaced and never shared.
The State of App Marketing in 2026
The landscape shifts rapidly. Looking at the last 18 months, here is what has changed:
The Fall of “Hyper-Casual”
The business model of “cheap users + spammy ads” is on the decline. High CPIs (Cost Per Install) mean you can no longer acquire a user for £0.20. The market has shifted to “Hybrid-Casual” and subscription-based apps that focus on deeper engagement and higher LTV.
AI-Driven Creative Testing
We are now seeing tools that utilise Generative AI to automatically produce hundreds of variations of ad copy and background visuals. The “Right Way” to market now involves automated A/B testing where algorithms decide which colour button works best, removing human bias from the equation.
Google’s Privacy Sandbox
Following Apple, Google is rolling out the Privacy Sandbox on Android. This will deprecate the GAID (Google Advertising ID). If you are relying solely on Android tracking because “Apple is too hard,” your grace period is coming to an end. You need to prepare for privacy-centric measurement on Android immediately.
Consultant’s Reality Check
I often have to have difficult conversations with clients regarding their budgets. A common scenario: A client comes to Inkbot Design seeking to invest £10,000 in a launch campaign for a new social app.
Here is the math I show them:
- Budget: £10,000
- CPI (Cost Per Install): £2.50 (Optimistic average)
- Installs: 4,000
- Retention (Day 30): 5% (Industry standard)
- Active Users after 1 Month: 200
They are left with 200 users. A social app with 200 users is a ghost town. The users leave because nobody is there. The money is gone.
The Lesson: If you have a limited budget, avoid launching a “network effect” app. Launch a utility app where a single user gets value even if they are the only person on earth using it. Fix your product mechanics before you pour gasoline on the fire.
For professional assistance in structuring your brand’s go-to-market strategy, consider our Digital Marketing Services.
The Verdict
App marketing is not magic. It is a discipline. It requires you to respect the platform guidelines, respect the user’s privacy, and most importantly, respect the user’s intelligence.
- Optimise ASO first. It is free traffic.
- Integrate an MMP. You cannot fly blind.
- Focus on Retention. Acquisition is vanity; retention is sanity.
- Test Creatives Relentlessly. The market gets bored fast.
If you are ready to stop guessing and start building a brand that survives the app store purge, you need a strategy that goes beyond the icon.
Frequently Asked Questions
What is the difference between ASO and SEO?
ASO (App Store Optimisation) focuses on ranking within app stores (Apple App Store, Google Play) to drive downloads. SEO (Search Engine Optimisation) focuses on ranking websites on search engines like Google. While keywords matter for both, ASO also relies heavily on visual conversion rates and uninstall data.
How much does it cost to market an app?
There is no fixed cost, but the average Cost Per Install (CPI) varies by region and category. In the UK/US, expect to pay between £2.00 and £5.00 per user for non-gaming apps. Gaming apps can be lower, while Fintech apps can exceed £10.00 per install.
What is an MMP, and why do I need one?
A Mobile Measurement Partner (MMP) like AppsFlyer or Adjust attributes app installs to specific marketing channels. Without an MMP, you cannot accurately tell if a user came from Facebook, Google, or an organic search, making it impossible to calculate ROI.
How does iOS 14.5 and IDFA affect app marketing?
It restricted the ability to track users across different apps and websites. Advertisers now receive less granular data, making it harder to target specific individuals. Marketers must now rely on aggregated data via Apple’s SKAdNetwork.
What is a good retention rate for an app?
Average retention rates are low. A “good” Day-1 retention is around 35-40%. By Day 30, seeing 5-10% of users still active is considered standard for many categories. Top-tier apps achieve significantly higher rates through the use of gamification and habit loops.
Can I market my app for free?
You can use organic strategies like ASO, social media content, and User Generated Content, but “free” costs time. To scale rapidly, paid acquisition is usually necessary to fuel the algorithms with initial data.
What is the K-factor in app growth?
The K-factor measures virality. It is the number of new users that each existing user invites. If your K-factor is 1.0, your user base is stable. If it is above 1.0, you are growing exponentially without paid ads.
Why are my app store conversion rates low?
Common causes include poor screenshots that fail to explain the benefit, a confusing icon, low star ratings (social proof), or targeting the wrong keywords (users arrive expecting one thing and see another).
Should I use Apple Search Ads?
Yes. Apple Search Ads often have the highest conversion rates because you are capturing users at the exact moment of intent—when they are searching for a keyword related to your app.
How do I reduce app uninstall rates?
Focus on the Onboarding experience (FTUE). Ensure the user sees value immediately. Avoid spamming push notifications. Regularly update the app to fix bugs, as technical instability is a primary driver of uninstalls.

